Chris Lawrence is a journalist and chief editor at Wlan Labs. He has been writing about technology for more than ten years. He writes about everything ranging from privacy to open source software. His goal is to educate readers about important topics to help make their lives easier.
Recently we’ve been asked what is onion over VPN and can it be beneficial? The Onion Over VPN feature was first introduced in Tor version 0.2.4.0 and allowed users to connect to the Tor network using a VPN service. The feature provides an extra layer of security and anonymity by hiding your true IP address and location from your websites.
How does the Onion network work?
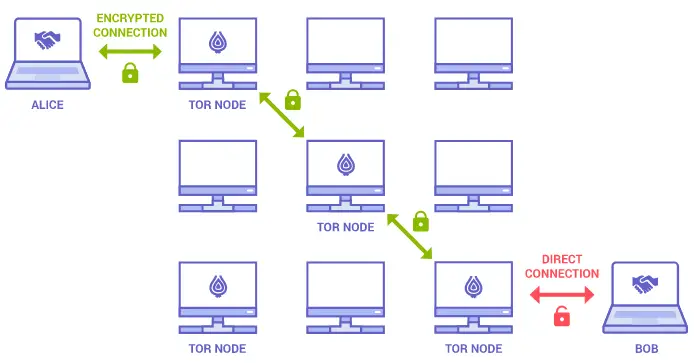
The Onion network is a collection of volunteer-operated servers that allow people to browse the internet anonymously. When you connect to the Onion network, your traffic is routed through various layers of security, making it very difficult for anyone to trace it back to you.
However, the downside is that it can make your internet connection slow and unreliable.
Is Onion over VPN safe?
Onion over VPN is a relatively safe way to browse the internet anonymously. However, it is important to remember that your VPN provider can still see your actual IP address and the websites you visit.
Do I need a VPN for Onion browser?
It depends on what you’re trying to accomplish. The Onion Browser is an anonymous web browser that routes traffic through the Tor network.
If you’re using it to anonymize your online activity, you need a VPN to protect your identity. However, a VPN isn’t necessary if you’re using it for privacy reasons (e.g., to keep websites from tracking you).
What are .onion domains?
.onion domains are websites that can only be accessed via the Tor network. They are usually only accessible through a special browser like the Tor Browser.
.onion domains are often used by criminals or others who wish to keep their identity and location secret for reasons of privacy or security. However, they can also be used for legitimate purposes such as journalism or political activism.
.onion domains are not like regular websites; they can be very difficult to find and access. They also tend to be quite unstable, with many .onion domains disappearing or changing addresses frequently.
Despite these challenges, .onion domains can be a valuable tool for those who need them. They offer a high degree of privacy and security and can be a great way to communicate and share information anonymously.
Onion over VPN encryption and traffic flow
When a user activates the onion over VPN feature, their traffic is sent through two VPN servers before exiting onto the internet. The traffic is first sent through an onion router, which encrypts the data multiple times.
This means that the data is encrypted twice, making it more difficult for someone to hack into or track the user’s traffic. The traffic is then transferred through a VPN server. This server decrypts the data and forwards it onto the internet. Using two VPN servers, the user’s traffic is encrypted and hidden from view. This can help protect against surveillance and tracking by websites.
There are a few drawbacks to using onion over VPN
- The first is that it can slow down the user’s internet connection.
- The second is that not all VPN providers offer the onion over VPN feature.
- It is important to research the different providers to find one that offers this feature.
What is CrowdStrike Falcon?
When it comes to security, there are many applications, and CrowdStrike is one of them. CrowdStrike Falcon is an endpoint security platform that provides organizations with real-time visibility and protection against threats.
The platform uses a combination of machine learning, artificial intelligence, and behavioral analytics to detect and prevent attacks. It also allows users to investigate and respond to incidents quickly.
Who Should Use Onion Over VPN?
Onion Over VPN is a good choice for anyone who wants to improve their privacy and security online. It is especially well-suited for people concerned about surveillance and tracking by government agencies or websites.
How to Use Onion Over VPN
- Choose a VPN provider that offers the Onion over VPN feature.
- Connect to the VPN server of your choice.
- Enable the Onion over VPN feature in your VPN client.
- Browse the internet anonymously!
Tor over VPN or VPN over Tor?
The Onion Router (Tor) is a free and open-source software project that helps you defend against traffic analysis, network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
Tor is used by millions of people worldwide to protect their privacy online and can be configured to connect to the Onion Over VPN feature. Tor works by encrypting your traffic and routing it through several random nodes on the Tor network before sending it to its final destination.
The debate between using Tor over VPN or VPN over Tor is contentious. Each has its advantages and disadvantages:
Tor over VPN:
Tor will encrypt your traffic before it passes through the VPN server, making it more difficult for your ISP or anyone else to snoop on your traffic. You will need to trust both your VPN provider and the TOR network not to spy on you. You may experience slower speeds due to the extra encryption.
VPN over Tor:
Your VPN provider will not be able to see what you are doing on the TOR network, but the TOR exit node could potentially spy on your traffic. You will need to trust the TOR network not to spy on you.
Which one you choose is up to you. Both have their advantages and disadvantages. However, if you are using a VPN over Tor, the VPN will encrypt your traffic before it passes through the exit node, making it more difficult for an attacker to spy on your traffic. If you are concerned about privacy and security, using both Tor and a VPN can give you the best of both worlds.
Risk of Malicious Exit Nodes
A VPN encrypts all web traffic between your computer and the VPN server. However, if the VPN server is compromised, the attacker could see all of your traffic. This is also true for Tor; if the exit node is compromised, the attacker could see all of your traffic.
Tor is a community-based project, and volunteers run exit nodes. This means there is no guarantee that an exit node is not compromised.
Access to Tor in Geo-Blocked Countries
Some countries, such as China and Iran, have blocked access to the Tor network, meaning people in these countries cannot use the Tor network to improve their privacy and security online.
If you are in a country where Tor is blocked, you can use a VPN over Tor to access the Tor network. By connecting to a VPN server in a country where Tor is not blocked, you will be able to access the Tor network and enhance privacy.
What Is NordVPN Onion Over VPN?
NordVPN Onion over VPN is a NordVPN server that is configured to work with the Tor network. This means that when you connect to the NordVPN server, your traffic will first be routed through the Tor network before it reaches the NordVPN server.
There are a few benefits to using NordVPN Onion over VPN. First, it can help you to bypass censorship and internet restrictions. Second, it can help to improve your privacy and security online. And third, it can help to improve your speed and performance when using the internet.
We’ve already discussed Tor above, but If you’re not familiar with the Tor network, it’s a free and open-source software that allows you to browse the internet anonymously.
When you use the Tor network, your traffic is routed through a series of volunteer-run servers around the world. This makes it very difficult for anyone to track your online activity or identify your real IP address.
NordVPN Onion over VPN is a great choice if you’re looking for a NordVPN server that can give you the benefits of the Tor network. However, it’s important to keep in mind that NordVPN Onion over VPN is not a perfect solution.
While it can help to improve your privacy and security, it’s important to remember that NordVPN is still a commercial VPN service. This means that NordVPN will still have access to your traffic data, and they may collect and store this data.
NordVPN also has a strict no-logs policy, so you can be sure that your traffic data will not be stored or monitored by NordVPN.
What Is Onion Over VPN Conclusion
We hope you’ve found our what is onion over VPN guide useful. According to recent studies, the onion routing protocol offers a number of advantages over traditional VPNs.
Onion routing is designed to provide anonymity and privacy by encrypting a user’s data traffic and routing it through a series of servers, or “onion layers.” This makes it difficult for anyone eavesdropping on the traffic to determine the originating source.
Additionally, onion routing is less susceptible to censorship than traditional VPNs. Because each layer in the network only knows the immediately previous and subsequent layers, any single node can be cut off from the network without disrupting communications.

